podman的基础设置和使用
Podman 是作为 libpod 库的一部分提供的实用程序。它可用于创建和维护容器。以下是Podman 执行一些基本命令
运行示例容器
因为容器在分离模式下运行,由命令中的-dpodman run表示,所以 Podman 将在运行后打印容器 ID。请注意,我们使用端口转发来访问 HTTP 服务器。为了成功运行,至少需要 slirp4netns v0.3.0。
[root@localhost ~]# podman run -dt -p 8080:8080/tcp -e HTTPD_VAR_RUN=/run/httpd -e HTTPD_MAIN_CONF_D_PATH=/etc/httpd/conf.d
-e HTTPD_MAIN_CONF_PATH=/etc/httpd/conf
-e HTTPD_CONTAINER_SCRIPTS_PATH=/usr/share/container-scripts/httpd/
registry.fedoraproject.org/f29/httpd /usr/bin/run-httpd
Trying to pull registry.fedoraproject.org/f29/httpd:latest...
Getting image source signatures
Copying blob d77ff9f653ce done
Copying blob aaf5ad2e1aa3 done
Copying blob 7692efc5f81c done
Copying config 25c76f9dcd done
Writing manifest to image destination
Storing signatures
364db788cd5751eb07bec9d6acabcfc5c2f4bc4f591c5e16e64d5ffb2b9aeb62
[root@localhost ~]# rpm -qa |grep slirp4netns
slirp4netns-1.1.8-1.module_el8.5.0+890+6b136101.x86_64
列出正在运行的容器
Podman ps命令用于列出创建和运行的容器。
[root@localhost ~]# podman ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
364db788cd57 registry.fedoraproject.org/f29/httpd:latest /usr/bin/run-http... 2 minutes ago Up 2 minutes ago 0.0.0.0:8080->8080/tcp festive_hermann
参数:
-a 或 --all //列出所有容器,包括未运行
-s 或 --size //查看本地机上所有运行实例的大小
-q 或 --quiet //查看容器id
检查正在运行的容器
您可以“检查”正在运行的容器以获取有关其自身的元数据和详细信息。我们甚至可以使用 inspect 子命令来查看分配给容器的 IP 地址。由于容器在无根模式下运行,因此未分配 IP 地址,并且该值将在 inspect 的输出中列为“无”。
[root@localhost ~]# podman inspect -l |grep -i ipaddress
"IPAddress": "10.88.0.2",
"IPAddress": "10.88.0.2",
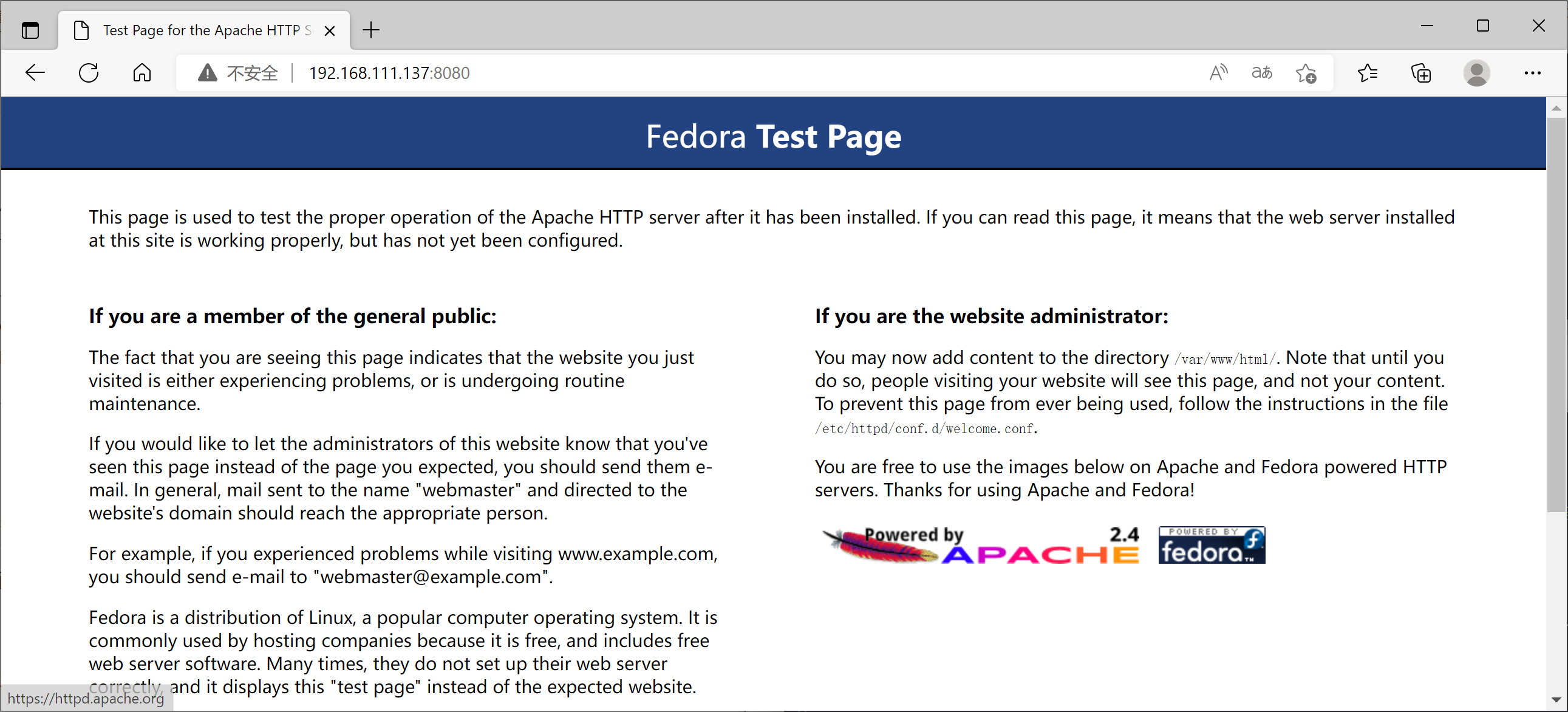
测试httpd服务器
由于我们没有容器的 IP 地址,我们可以使用 curl 测试宿主操作系统和容器之间的网络通信。以下命令应该显示我们容器化 httpd 服务器的索引页面。
[root@localhost ~]# curl 10.88.0.2:8080 //需要跟8080端口号
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.1//EN" "http://www.w3.org/TR/xhtml11/DTD/xhtml11.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" xml:lang="en" lang="en">
<head>
<title>Test Page for the Apache HTTP Server on Fedora</title>
<meta http-equiv="Content-Type" content="text/html; charset=UTF-8" />
通过宿主机加上映射出来的端口进行访问
查看容器的日志
您也可以使用 Podman 查看容器的日志:
[root@localhost ~]# podman logs -l
=> sourcing 10-set-mpm.sh ...
=> sourcing 20-copy-config.sh ...
=> sourcing 40-ssl-certs.sh ...
AH00558: httpd: Could not reliably determine the server's fully qualified domain name, using 10.88.0.2. Set the 'ServerName' directive globally to suppress this message
[Mon Aug 15 15:20:46.005433 2022] [ssl:warn] [pid 1:tid 139972014361984] AH01882: Init: this version of mod_ssl was compiled against a newer library (OpenSSL 1.1.1b FIPS 26 Feb 2019, version currently loaded is OpenSSL 1.1.1 FIPS 11 Sep 2018) - may result in undefined or erroneous behavior
[Mon Aug 15 15:20:46.006165 2022] [ssl:warn] [pid 1:tid 139972014361984] AH01909: 10.88.0.2:8443:0 server certificate does NOT include an ID which matches the server name
查看容器进程pid
您可以使用top观察容器中的 httpd pid 。
[root@localhost ~]# podman top -l
USER PID PPID %CPU ELAPSED TTY TIME COMMAND
default 1 0 0.000 9m46.752864551s pts/0 0s httpd -D FOREGROUND
default 23 1 0.000 9m46.753000255s pts/0 0s /usr/bin/coreutils --coreutils-prog-shebang=cat /usr/bin/cat
default 24 1 0.000 9m46.753028749s pts/0 0s /usr/bin/coreutils --coreutils-prog-shebang=cat /usr/bin/cat
default 25 1 0.000 9m46.753057272s pts/0 0s /usr/bin/coreutils --coreutils-prog-shebang=cat /usr/bin/cat
default 26 1 0.000 9m46.753080013s pts/0 0s /usr/bin/coreutils --coreutils-prog-shebang=cat /usr/bin/cat
default 27 1 0.000 9m46.753102749s pts/0 0s httpd -D FOREGROUND
default 28 1 0.000 9m46.753125034s pts/0 0s httpd -D FOREGROUND
default 32 1 0.000 9m46.753148102s pts/0 0s httpd -D FOREGROUND
default 47 1 0.000 9m46.753176176s pts/0 0s httpd -D FOREGROUND
对容器执行检查操作
检查点容器会停止容器,同时将容器中所有进程的状态写入磁盘。有了这个,容器可以稍后恢复并在与检查点完全相同的时间点继续运行。此功能需要在系统上安装 CRIU 3.11 或更高版本。此功能不支持为无根;因此,如果您想尝试它,您需要以 root 身份重新创建您的容器,使用相同的命令但使用 sudo。
[root@localhost ~]# podman container checkpoint festive_hermann
364db788cd5751eb07bec9d6acabcfc5c2f4bc4f591c5e16e64d5ffb2b9aeb62
[root@localhost ~]# podman ps -a
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
364db788cd57 registry.fedoraproject.org/f29/httpd:latest /usr/bin/run-http... 20 minutes ago Exited (0) 8 seconds ago 0.0.0.0:8080->8080/tcp festive_hermann
还原容器
还原容器仅适用于以前检查点的容器。还原的容器将继续在检查点操作的同一时间点运行。要恢复容器
[root@localhost ~]# podman container restore festive_hermann
364db788cd5751eb07bec9d6acabcfc5c2f4bc4f591c5e16e64d5ffb2b9aeb62
[root@localhost ~]# podman ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
364db788cd57 registry.fedoraproject.org/f29/httpd:latest /usr/bin/run-http... 21 minutes ago Up 21 minutes ago 0.0.0.0:8080->8080/tcp festive_hermann
还原后,然后容器将像检查点之前一样再次应答请求
[root@localhost ~]# curl 10.88.0.2:8080
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.1//EN" "http://www.w3.org/TR/xhtml11/DTD/xhtml11.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" xml:lang="en" lang="en">
<head>
<title>Test Page for the Apache HTTP Server on Fedora</title>
<meta http-equiv="Content-Type" content="text/html; charset=UTF-8" />
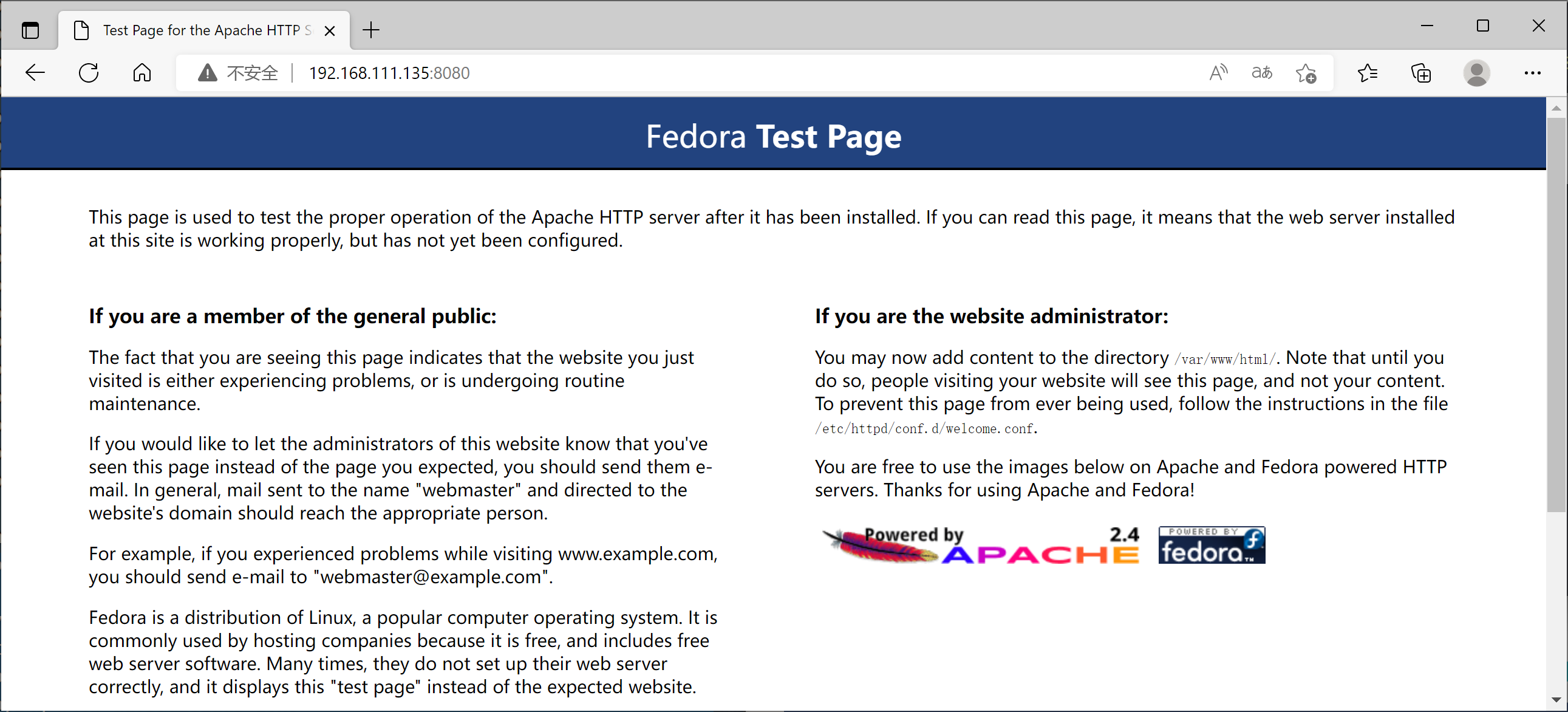
迁移容器
要将容器从一个主机实时迁移到另一个主机,容器将在迁移的源系统上执行检查点操作,传输到目标系统,然后在目标系统上还原。传输检查点时,可以指定输出文件。
在源系统上:
[root@localhost ~]# podman container checkpoint festive_hermann -e /tmp/checkpoint.tar.gz
364db788cd5751eb07bec9d6acabcfc5c2f4bc4f591c5e16e64d5ffb2b9aeb62
//传输到检查点上
[root@localhost ~]# scp /tmp/checkpoint.tar.gz 192.168.111.135:/tmp
The authenticity of host '192.168.111.135 (192.168.111.135)' can't be established.
ECDSA key fingerprint is SHA256:AneDLcALQuLH7WhrvDCtu+7mdCXjrXa87i7CQ+01ntk.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.111.135' (ECDSA) to the list of known hosts.
root@192.168.111.135's password:
checkpoint.tar.gz 100% 4307KB 58.9MB/s 00:00
在目标容器上:
[root@localhost ~]# podman container restore -i /tmp/checkpoint.tar.gz
Trying to pull registry.fedoraproject.org/f29/httpd:latest...
Getting image source signatures
Copying blob d77ff9f653ce done
Copying blob aaf5ad2e1aa3 done
Copying blob 7692efc5f81c done
Copying config 25c76f9dcd done
Writing manifest to image destination
Storing signatures
364db788cd5751eb07bec9d6acabcfc5c2f4bc4f591c5e16e64d5ffb2b9aeb62
访问一下
停止容器
要停止httpd容器
[root@localhost ~]# podman stop -l
364db788cd5751eb07bec9d6acabcfc5c2f4bc4f591c5e16e64d5ffb2b9aeb62
[root@localhost ~]# podman ps -a
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
364db788cd57 registry.fedoraproject.org/f29/httpd:latest /usr/bin/run-http... About a minute ago Exited (0) 6 seconds ago 0.0.0.0:8080->8080/tcp festive_hermann
移除容器
删除httpd容器
[root@localhost ~]# podman rm -l
364db788cd5751eb07bec9d6acabcfc5c2f4bc4f591c5e16e64d5ffb2b9aeb62
[root@localhost ~]# podman ps -a
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
podman签发和分发容器镜像并推送到harbor仓库中
对容器映像进行签名源于仅信任专用映像提供程序的动机,以缓解中间人 (MITM) 攻击或对容器注册表的攻击。对图像进行签名的一种方法是使用 GNU 隐私卫士 (GPG) 密钥。此技术通常与任何符合 OCI 的容器注册表(如 Quay.io)兼容。值得一提的是,OpenShift 集成容器注册表开箱即用地支持这种签名机制,这使得单独的签名存储变得不必要。
从技术角度来看,我们可以在将映像推送到远程注册表之前利用 Podman 对映像进行签名。之后,所有运行Podman的系统都必须配置为从远程服务器检索签名,远程服务器可以是任何简单的Web服务器。这意味着在映像拉取操作期间,每个未签名的映像都将被拒绝。但是这是如何工作的呢?
首先,我们必须创建一个GPG密钥对或选择一个本地可用的密钥对。要生成新的GPG密钥,只需运行并按照交互式对话框进行操作即可。现在我们应该能够验证密钥是否在本地存在:
生成GPG密钥
[root@localhost ~]# gpg --full-gen-key
gpg (GnuPG) 2.2.20; Copyright (C) 2020 Free Software Foundation, Inc.
This is free software: you are free to change and redistribute it.
There is NO WARRANTY, to the extent permitted by law.
gpg: directory '/root/.gnupg' created
gpg: keybox '/root/.gnupg/pubring.kbx' created
Please select what kind of key you want:
(1) RSA and RSA (default)
(2) DSA and Elgamal
(3) DSA (sign only)
(4) RSA (sign only)
(14) Existing key from card
Your selection? //默认回车
RSA keys may be between 1024 and 4096 bits long.
What keysize do you want? (2048) //默认回车
Requested keysize is 2048 bits
Please specify how long the key should be valid.
0 = key does not expire
<n> = key expires in n days
<n>w = key expires in n weeks
<n>m = key expires in n months
<n>y = key expires in n years
Key is valid for? (0) //默认回车
Key does not expire at all
Is this correct? (y/N) y
GnuPG needs to construct a user ID to identify your key.
Real name: zxr@123.com //姓名
Email address: zxr@123.com //邮箱
Comment: abc //描述
You selected this USER-ID:
"zxr@123.com (abc) <zxr@123.com>"
Change (N)ame, (C)omment, (E)mail or (O)kay/(Q)uit? o
┌─┐
│ Please enter the passphrase to │
│ protect your new key │
│ │
│ Passphrase: ***********
│ │
│ <OK> <Cancel> │
└─┘
┌─┐
│ Please re-enter this passphrase │
│ │
│ Passphrase: ***********
│ │
│ <OK> <Cancel> │
└─┘
We need to generate a lot of random bytes. It is a good idea to perform
some other action (type on the keyboard, move the mouse, utilize the
disks) during the prime generation; this gives the random number
generator a better chance to gain enough entropy.
We need to generate a lot of random bytes. It is a good idea to perform
some other action (type on the keyboard, move the mouse, utilize the
disks) during the prime generation; this gives the random number
generator a better chance to gain enough entropy.
gpg: /root/.gnupg/trustdb.gpg: trustdb created
gpg: key 00A1D061CDEE80BC marked as ultimately trusted
gpg: directory '/root/.gnupg/openpgp-revocs.d' created
gpg: revocation certificate stored as '/root/.gnupg/openpgp-revocs.d/BB4A9DEFDEEE44DB806410A100A1D061CDEE80BC.rev'
public and secret key created and signed.
pub rsa2048 2022-08-16 [SC]
BB4A9DEFDEEE44DB806410A100A1D061CDEE80BC
uid zxr@123.com (abc) <zxr@123.com>
sub rsa2048 2022-08-16 [E]
查看密钥
[root@localhost ~]# gpg --list-keys zxr@123.com
gpg: checking the trustdb
gpg: marginals needed: 3 completes needed: 1 trust model: pgp
gpg: depth: 0 valid: 1 signed: 0 trust: 0-, 0q, 0n, 0m, 0f, 1u
pub rsa2048 2022-08-16 [SC]
BB4A9DEFDEEE44DB806410A100A1D061CDEE80BC
uid [ultimate] zxr@123.com (abc) <zxr@123.com>
sub rsa2048 2022-08-16 [E]
部署私有仓库
有两种
-
一种在另一台主机上部署harbor私有仓库
-
直接在本机部署私有仓库
在本机上部署私有仓库
拉取alpine镜像作为测试的镜像
[root@localhost ~]# podman pull docker://docker.io/alpine:latest
Trying to pull docker.io/library/alpine:latest...
Getting image source signatures
Copying blob 59bf1c3509f3 done
Copying config c059bfaa84 done
Writing manifest to image destination
Storing signatures
c059bfaa849c4d8e4aecaeb3a10c2d9b3d85f5165c66ad3a4d937758128c4d18
运行一个容器
[root@localhost ~]# podman run -d -p 5000:5000 docker.io/registry
Trying to pull docker.io/library/registry:latest...
Getting image source signatures
Copying blob e2ead8259a04 done
Copying blob 79e9f2f55bf5 done
Copying blob 3790aef225b9 done
Copying blob 0d96da54f60b done
Copying blob 5b27040df4a2 done
Copying config b8604a3fe8 done
Writing manifest to image destination
Storing signatures
f46f985d117bfd8b9e95509534d74a74b969dfcde4dbea65180ac8e099631e45
给alpine打个标签指向本地仓库
[root@localhost ~]# podman tag alpine localhost:5000/alpine
[root@localhost ~]# podman images alpine
REPOSITORY TAG IMAGE ID CREATED SIZE
docker.io/library/alpine latest c059bfaa849c 8 months ago 5.87 MB
localhost:5000/alpine latest c059bfaa849c 8 months ago 5.87 MB
为了让镜像能上传至本地的私有仓库,修改/etc/containers/registries.d/default.yaml文件
我们可以看到我们配置了两个签名存储:
sigstore: 引用 Web 服务器进行签名读取sigstore-staging: 引用文件路径进行签名写入
[root@localhost ~]# vim /etc/containers/registries.d/default.yaml
default-docker:
# sigstore: file:///var/lib/containers/sigstore
sigstore: http://localhost:8000 //添加这一行
sigstore-staging: file:///var/lib/containers/sigstore
推送并签署镜像
//生成目录
[root@localhost ~]# GNUPGHOME=$HOME/.gnupg
//推送镜像
[root@localhost ~]# podman push --tls-verify=false --sign-by zxr@123.com localhost:5000/alpine:latest
Getting image source signatures
Copying blob 8d3ac3489996 done
Copying config c059bfaa84 done
Writing manifest to image destination
Signing manifest
Storing signatures
┌─┐
│ Please enter the passphrase to unlock the OpenPGP secret key: │
│ "zxr@123.com (abc) <zxr@123.com>" │
│ 2048-bit RSA key, ID 00A1D061CDEE80BC, │
│ created 2022-08-16. │
│ │
│ │
│ Passphrase: ***********
│ │
│ <OK> <Cancel> │
└─┘
查看签名存放位置
[root@localhost ~]# ls /var/lib/containers/sigstore/
'alpine@sha256=964248be4bb8e3052c8b411271126f70c5c5015df31e014bfc41fad50edf78d8'
开启另一个终端跑web服务
[root@localhost ~]# dnf -y module install python38
[root@localhost ~]# cd /var/lib/containers/sigstore/
[root@localhost sigstore]# python3 -m http.server
Serving HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) ...
编写一个策略来强制签名必须有效
[root@localhost ~]# vim /etc/containers/policy.json
{
"default": [
{
"type": "insecureAcceptAnything"
}
],
"transports": {
"docker": {
"localhost:5000": [ //修改
{
"type": "signedBy",
"keyType": "GPGKeys",
"keyPath": "/tmp/key.gpg"
}
keypath还不存在,因此我们必须将GPG密钥放在/tmp下
[root@localhost ~]# gpg --output /tmp/key.gpg --armor --export zxr@123.com
拉取镜像验证
//先删除
[root@localhost ~]# podman rmi localhost:5000/alpine:latest
Untagged: localhost:5000/alpine:latest
//拉取镜像
[root@localhost ~]# podman pull --tls-verify=false localhost:5000/alpine
Trying to pull localhost:5000/alpine:latest...
Getting image source signatures
Checking if image destination supports signatures
Copying blob 3c4e9198e8c1 [--------------------------------------] 0.0b / 0.0b
Copying config c059bfaa84 done
Writing manifest to image destination
Storing signatures
c059bfaa849c4d8e4aecaeb3a10c2d9b3d85f5165c66ad3a4d937758128c4d18
然后去另一个终端查看web服务器的日志
[root@localhost sigstore]# python3 -m http.server
Serving HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) ...
127.0.0.1 - - [16/Aug/2022 13:40:53] "GET /alpine@sha256=964248be4bb8e3052c8b411271126f70c5c5015df31e014bfc41fad50edf78d8/signature-1 HTTP/1.1" 200 -
127.0.0.1 - - [16/Aug/2022 13:40:53] code 404, message File not found
127.0.0.1 - - [16/Aug/2022 13:40:53] "GET /alpine@sha256=964248be4bb8e3052c8b411271126f70c5c5015df31e014bfc41fad50edf78d8/signature-2 HTTP/1.1" 404 -
127.0.0.1 - - [16/Aug/2022 13:43:19] "GET /alpine@sha256=964248be4bb8e3052c8b411271126f70c5c5015df31e014bfc41fad50edf78d8/signature-1 HTTP/1.1" 200 -
127.0.0.1 - - [16/Aug/2022 13:43:19] code 404, message File not found
127.0.0.1 - - [16/Aug/2022 13:43:19] "GET /alpine@sha256=964248be4bb8e3052c8b411271126f70c5c5015df31e014bfc41fad50edf78d8/signature-2 HTTP/1.1" 404 -
文章来源: 博客园
- 还没有人评论,欢迎说说您的想法!





 客服
客服


